WazirX: How North Korea Stole $235 Million from Indian Crypto Users — and Nobody Will Pay
On July 18, 2024, at 9:04 AM Mumbai time, someone began draining WazirX's largest wallet. Twenty-six minutes later, $235 million was gone. As of January 2026, users are holding non-tradeable tokens. The perpetrators are in Pyongyang.

1. The Heist
Mumbai, July 18, 2024. WazirX is India's largest crypto exchange — tens of millions of registered users, the entry point for crypto in one of the world's youngest populations.
At 9:04 AM, a multi-signature wallet authorized to manage platform reserves starts emptying. Token after token: SHIB, ETH, MATIC, PEPE. The pace is mechanical, fast, precise. Twenty-six minutes. $235 million transferred to anonymous addresses.
Users are browsing normally the whole time. Apps display balances as usual. At 1:00 PM, WazirX suspends withdrawals with a brief notice citing "technical issues." Hours later comes the confirmation: "We are aware that one of our multisig wallets has been compromised."
It was the second-largest hack in crypto history, behind only the $625 million Ronin Network theft in 2022. The key difference: Axie Infinity and Sky Mavis reimbursed their users. WazirX did not.
2. Anatomy of the Attack
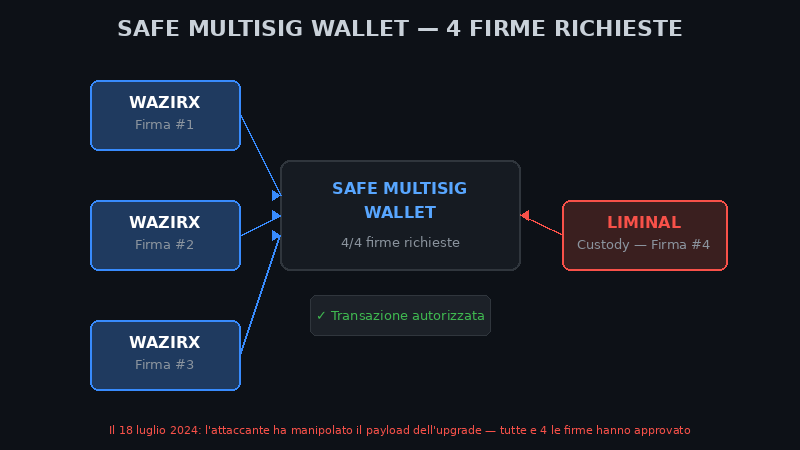
The targeted wallet was a Safe multisig. Safe requires multiple digital signatures from separate devices to authorize any outgoing transaction. Three of the four required signatures belonged to WazirX. The fourth belonged to Liminal Custody, a third-party custodian chosen to strengthen operational security.
The attackers exploited Safe's contract upgrade mechanism. They crafted an upgrade transaction with a malicious payload: instead of updating the contract with legitimate code, the new implementation transferred full control of the wallet to the attackers. When the authorized signers approved what appeared to be routine maintenance, they were signing their own undoing.
All four signatures approved. The funds left.
Chainalysis, Elliptic, ZachXBT, and Mandiant all analyzed the attack. The three WazirX hardware devices used for signing were clean — no compromise detected on those. The manipulation had happened upstream, in the display layer that showed signers the transaction they were approving.
3. The Ghost Signature — Liminal Custody's Role
Liminal Custody controlled the fourth signature. But it also controlled something more relevant: the interface platform that WazirX used to view and approve outgoing transactions. WazirX signers saw what Liminal's interface showed them — not what was actually happening on-chain.
On October 22, 2024 — 75 days after the hack — Liminal disclosed a detail that should have generated more headlines: WazirX still had $175 million deposited on its platform. Of that, roughly $50 million was under WazirX's direct control. An exchange just robbed of $235 million, still using the same custodian for hundreds of millions of dollars.
In September 2024, Liminal commissioned a Grant Thornton audit. The finding: Liminal's infrastructure was intact. The breach originated on the "client side" — meaning WazirX. WazirX founder Nischal Shetty responded to TheStreet directly: "The cyber attack was not on the infrastructure of WazirX. It was a website we were using for managing these funds — Liminal's platform. We don't know what was happening behind the scenes of a different website."
Two audits. Two opposite conclusions. Each commissioned by the party it was designed to exonerate.
4. The Lazarus Group — When Pyongyang Is Behind It
The FBI, Chainalysis, and ZachXBT attributed the attack to the Lazarus Group — the hacker unit of North Korean military intelligence (RGB, Reconnaissance General Bureau).
Between 2017 and 2024, Lazarus stole over $3 billion in cryptocurrency, according to US Treasury estimates. Those funds finance Kim Jong-un's nuclear and missile program, circumventing international sanctions. This is not speculation: it is the conclusion of parallel investigations by the FBI, the UN, and the US Treasury Department, backed by verifiable on-chain analysis.
Their method is documented and consistent. Months of preparation: infiltrating target organizations through fake job interviews with software engineers — the same technique used in the Ronin attack — installing malware through files shared during interviews, mapping the infrastructure, identifying weak points in the signing process. Then execution during a moment of low operational vigilance.
The funds stolen from WazirX followed the standard Lazarus route: intermediate wallets, then Tornado Cash — the Ethereum mixer sanctioned by OFAC in 2022. From Tornado Cash, the funds disperse through thousands of micro-transactions toward clean wallets. $235 million. Recovered: zero.
5. Socializing the Losses — Who Actually Paid
WazirX did not file for bankruptcy. It did something more subtle.
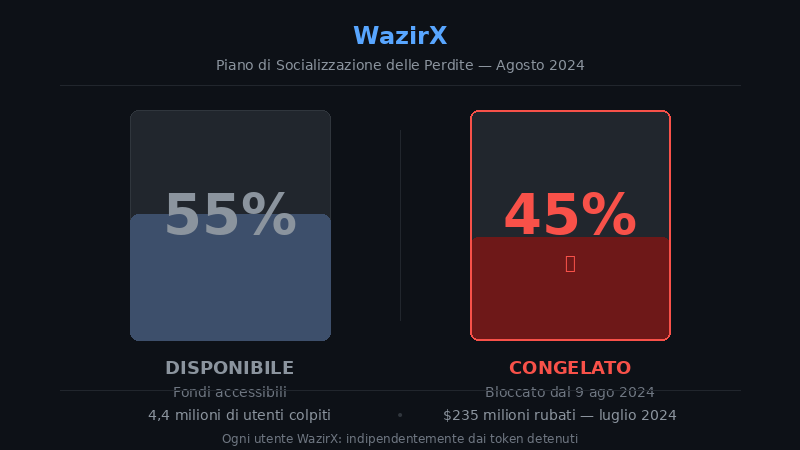
On August 9, 2024 — three weeks after the hack — the exchange published a "loss socialization" plan. 45% of every user's balance was frozen immediately. Someone with $10,000 on WazirX could access $5,500. The remaining $4,500 was locked pending a recovery plan still to be defined.
The logic: the $235 million loss gets distributed proportionally across the entire user base rather than concentrated on holders of the specific stolen tokens. A form of forced risk mutualization.
The problem: a user holding only USDT or Bitcoin on WazirX — assets untouched by the hack — ended up with 45% of their funds frozen anyway. Their loss was not operational. It was imposed.
Indian crypto forums, subreddits, Twitter threads: the user response was anger. Thousands of posts. Petitions. Complaints. One Reddit India user documented having the equivalent of roughly $45,000 frozen. Their only remaining option was joining a collective action through the Singapore proceedings — estimated participation costs higher than what they would likely recover.

6. Singapore, Recovery Tokens, and Impossible Justice
WazirX operates through Zettai Pte Ltd, a Singapore-registered company. On August 28, 2024, it filed for moratorium protection with the Singapore High Court, which was granted on September 27, 2024.
In parallel, 54 hack victims brought the case to India's Supreme Court. On April 16, 2025, Justices Gavai and Masih rejected the petition: cryptocurrency regulation is a policy matter, not a judicial one. As early as March 2025, the NCDRC had already dismissed a separate case. For 4.4 million affected users, the Indian judiciary delivered a single message: handle it yourselves.
The restructuring plan approved in April 2025 received 93.1% creditor approval. 83% of non-stolen funds are redistributed immediately; the rest comes in the form of Recovery Tokens, distributed in January 2026.
Three structural problems the plan does not fix: Recovery Tokens are not tradeable on any exchange — zero liquidity, zero independent market price. They are revalued every three months by WazirX itself, with no external mechanism. The plan guarantees no minimum recovery percentage: if WazirX does not generate sufficient resources, the tokens pay nothing.
Indian users seeking to assert their rights as foreign creditors of a Singaporean company must navigate international legal proceedings — costs prohibitive relative to the amounts lost by most retail participants.
7. The Blame Game — Who Hasn't Told the Full Story
Nearly two years after the hack, five questions remain without credible public answers.
How much did WazirX management know before informing users? The attack began at 9:04 AM. Withdrawals were suspended at 1:00 PM. Four hours during which the exchange was technically operational — and some users deposited funds.
Why did Liminal's interface show data inconsistent with the blockchain? If WazirX signers saw a legitimate transaction on screen while something different was happening on-chain, the point of compromise was in the interface. Liminal has not published verifiable technical logs related to the incident.
Who approved the Safe contract upgrade, and under what procedure? A smart contract upgrade is a high-risk operation. WazirX's internal process for this type of transaction has never been made public.
Was the Singapore structure designed to shield the company from creditors? The moratorium blocked user legal actions for over a year while WazirX operated and built its plan in relative peace.
Who actually controlled WazirX at the time of the hack? In December 2025, Nischal Shetty confirmed to TheStreet that the ownership dispute with Binance is in formal litigation. Binance maintains the 2019 acquisition was never finalized. Shetty calls it "he said, she said" and refused to say whether Binance reached out after the hack, citing the ongoing litigation. If the ownership structure was contested at the time of the breach, who held final authority over operational decisions?
WazirX and Liminal are still trading accusations. Neither has faced significant legal consequences. No executive has been charged in any jurisdiction.
8. Investigative Conclusion
The WazirX theft illustrates something worth understanding clearly.
The Safe protocol had no vulnerabilities. The Ethereum blockchain was not compromised. The cryptography behind digital signatures worked exactly as designed. The attack succeeded because it exploited the human and infrastructural layer sitting above the technology: the interface displaying the transactions, the internal review process, the trust between business partners.
Lazarus Group stole $235 million without touching a single cryptographic algorithm. They manipulated what people saw on their screens.
As of January 2026, WazirX users hold Recovery Tokens whose value depends entirely on the operational future of a company that just suffered the second-largest crypto theft in history. Lazarus Group has already converted the funds. North Korea's missile program received a liquidity injection.
Liminal and WazirX are still arguing. Creditors are still waiting. The story repeats every year — different exchange name, same attack mechanism — because the lesson is uncomfortable: whoever holds your private keys holds your funds. The only real protection against the next WazirX is not having a next WazirX to trust.
Learn more: Safe WazirX Alternatives 2026 | Best Bitcoin exchanges 2026 | DAC8 Crypto Tax Reporting EU 2026 | Bitcoin ETP on stock market